- Banking
- Business Services
- Chemical, Agriculture, Mining
- Computer & Technology
- Construction & Engineering
- Development Tools
- Education
- Energy & Utilities
- Financial Services
- Food & Beverage
- Foundations & Non-Profits
- Government
- Healthcare
- Insurance
- Manufacturing
- Pharma & Biotech
- Retail & Wholesale
- Telecommunications
- Transportation & Logistics
- Travel, Leisure, Entertainment
- Advertising, Media, Publishing
- Other Industries
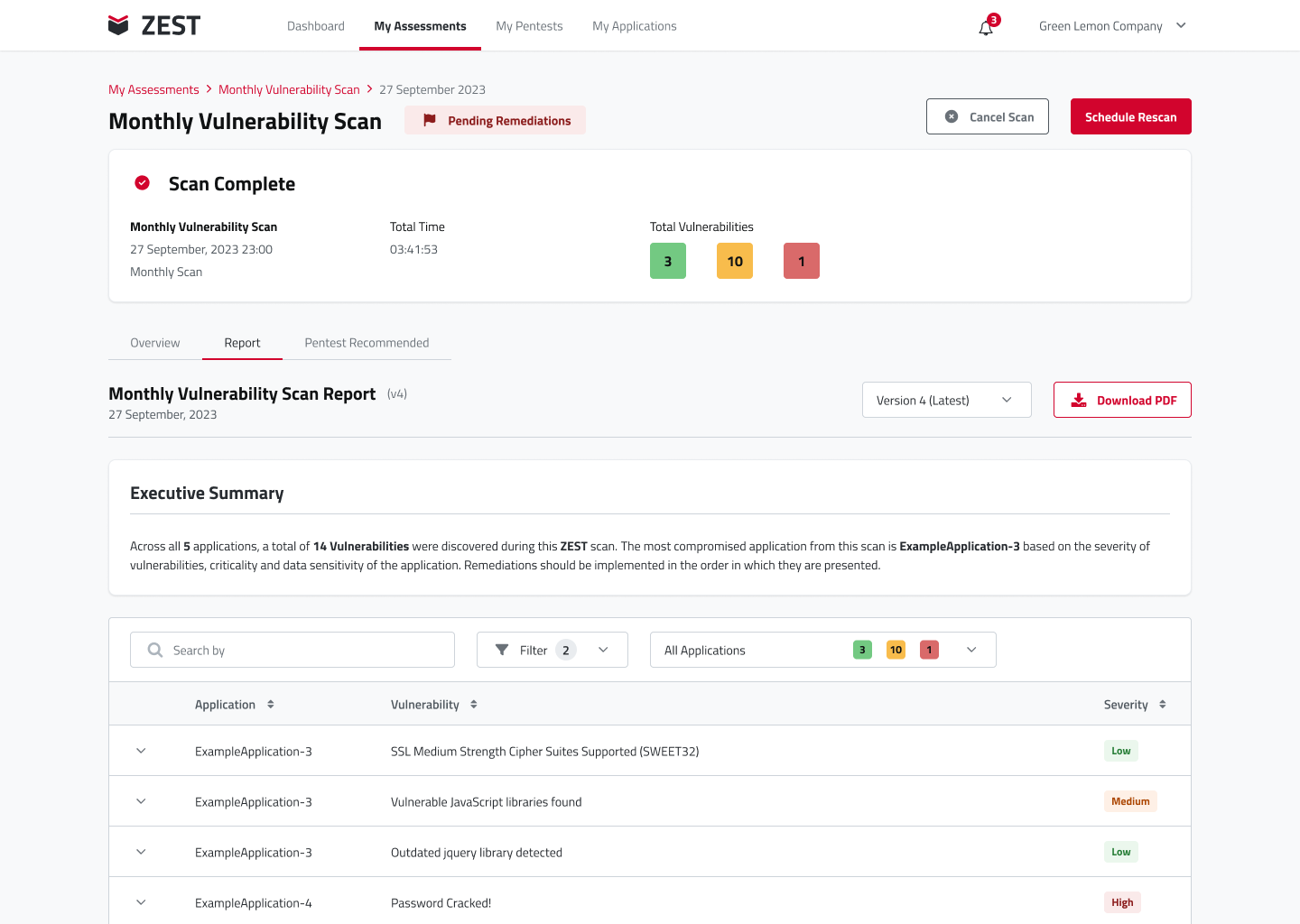
Solution Overview
Key Features
Key Features
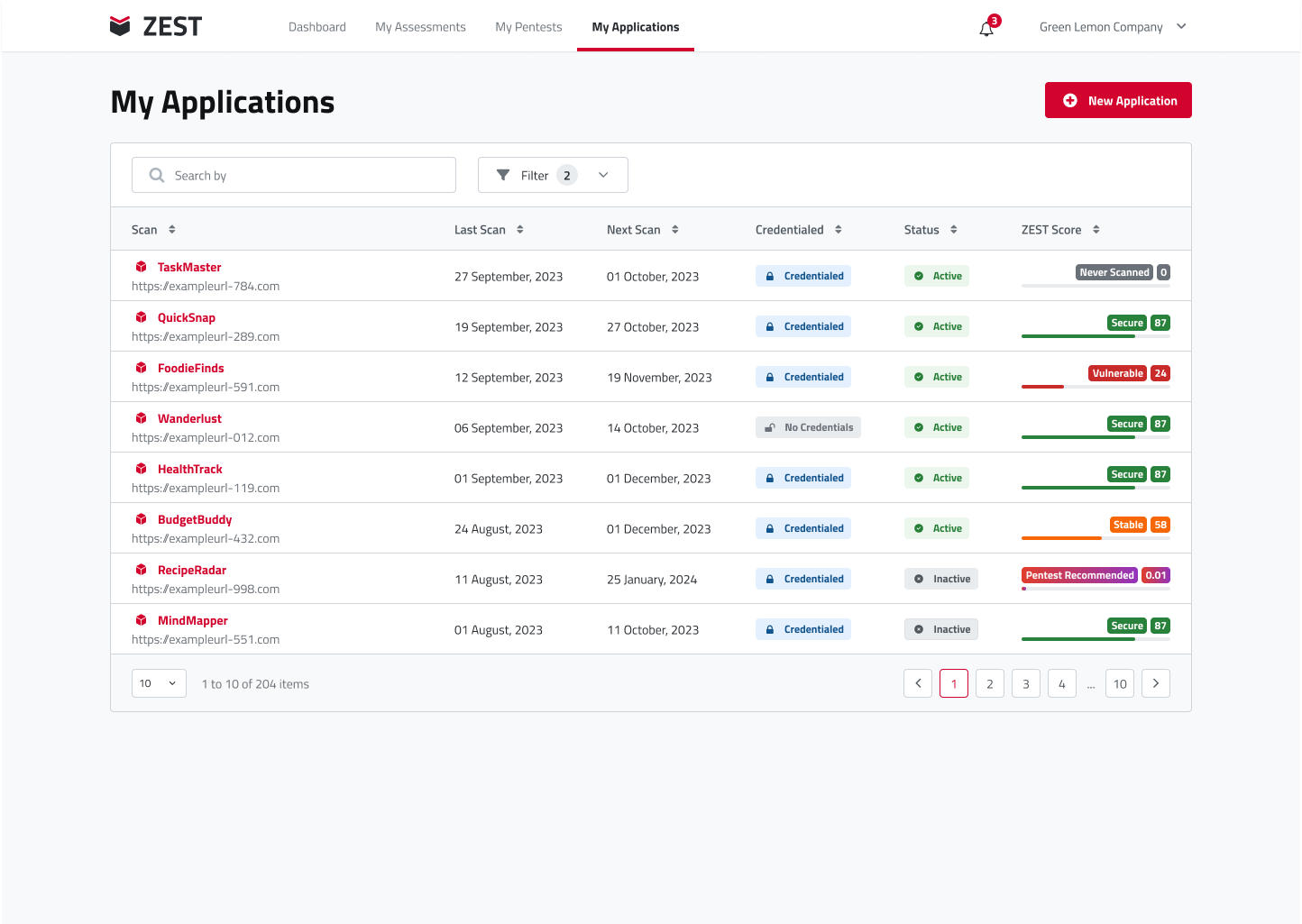
- Centralised security management: A one-stop solution to monitor and increase the security posture of all applications and assets from a unified interface.
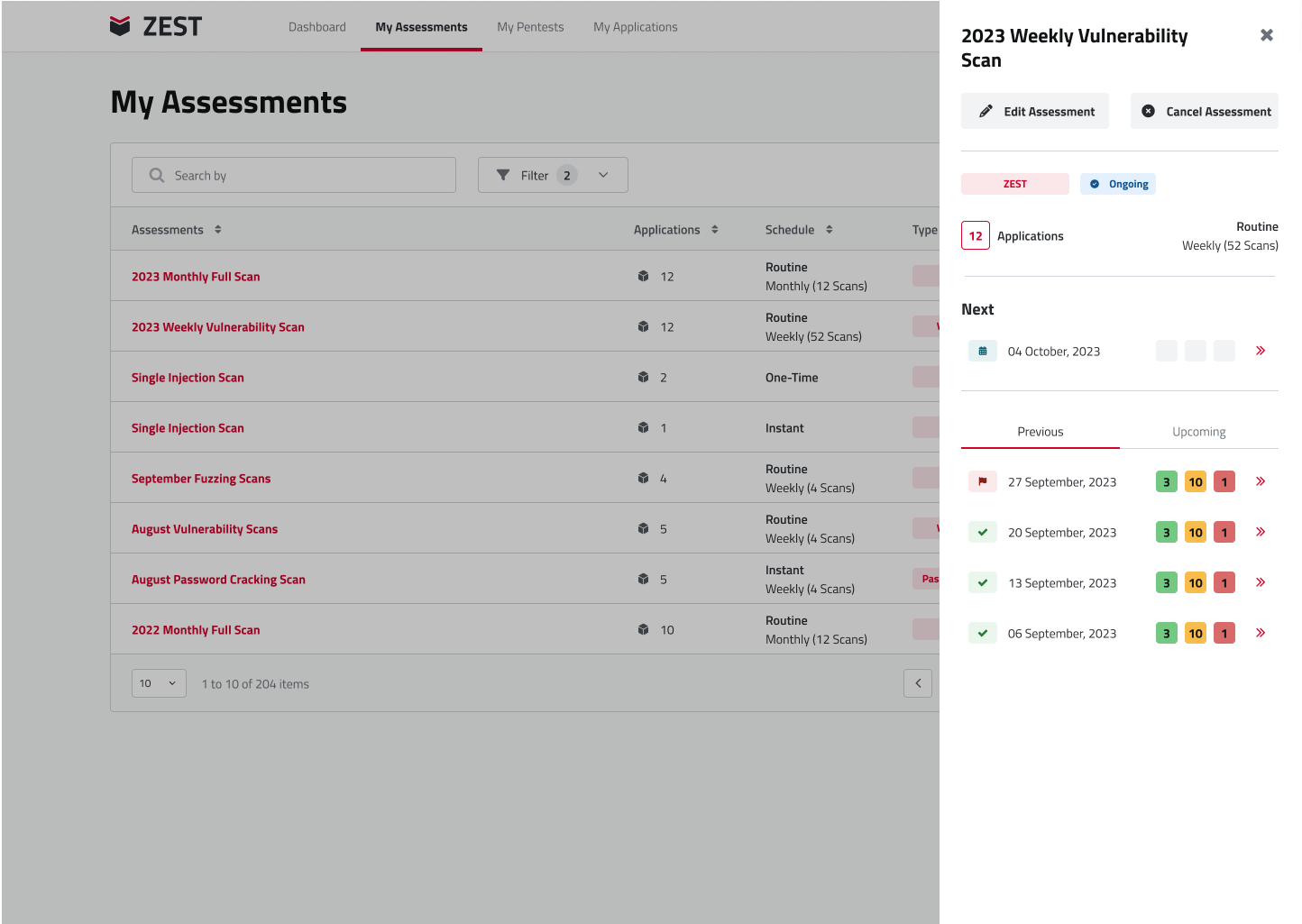
- Easy configuration: Configure one or a group of applications, for one time, or repeated scanning.
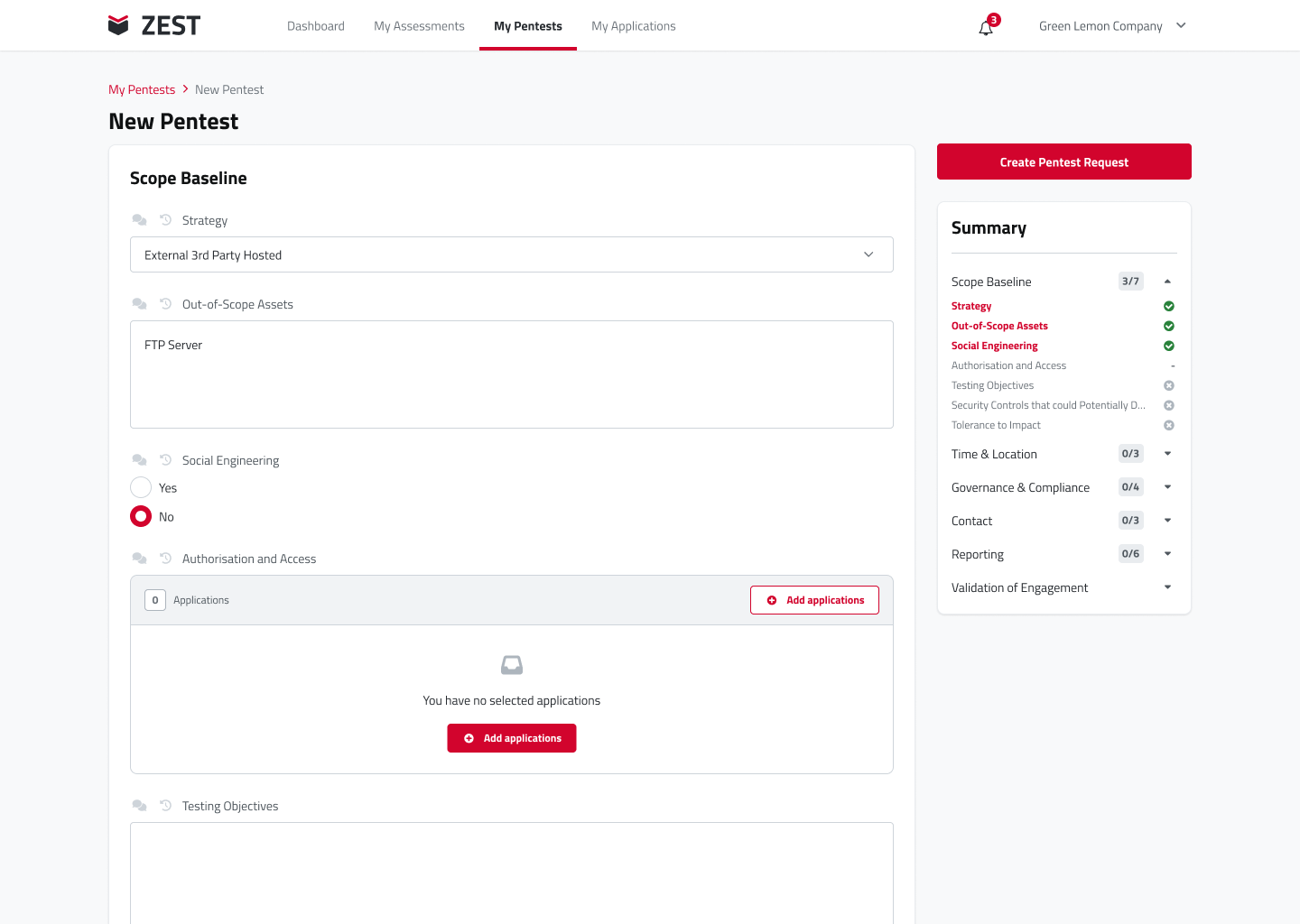
- Fully customisable: Pick and choose the tools you want to be part of your assessment.
- Simple reporting: Gauge the security of your assets with an advanced scoring system
- Full stack scanning: Comprehensive vulnerability scanning that covers Web applications, SAST & DAST, API’s, infrastructure and more.
- Custom scanning: Have your own or preferred tools? Integrate them into ZEST to align with your requirements.
- Hosting: On-Cloud, or on Premise.
- AI Enhanced: ZEST uses the power of AI to reduce false positives, normalised reporting, and prioritise vulnerabilities based on related vulnerabilities.
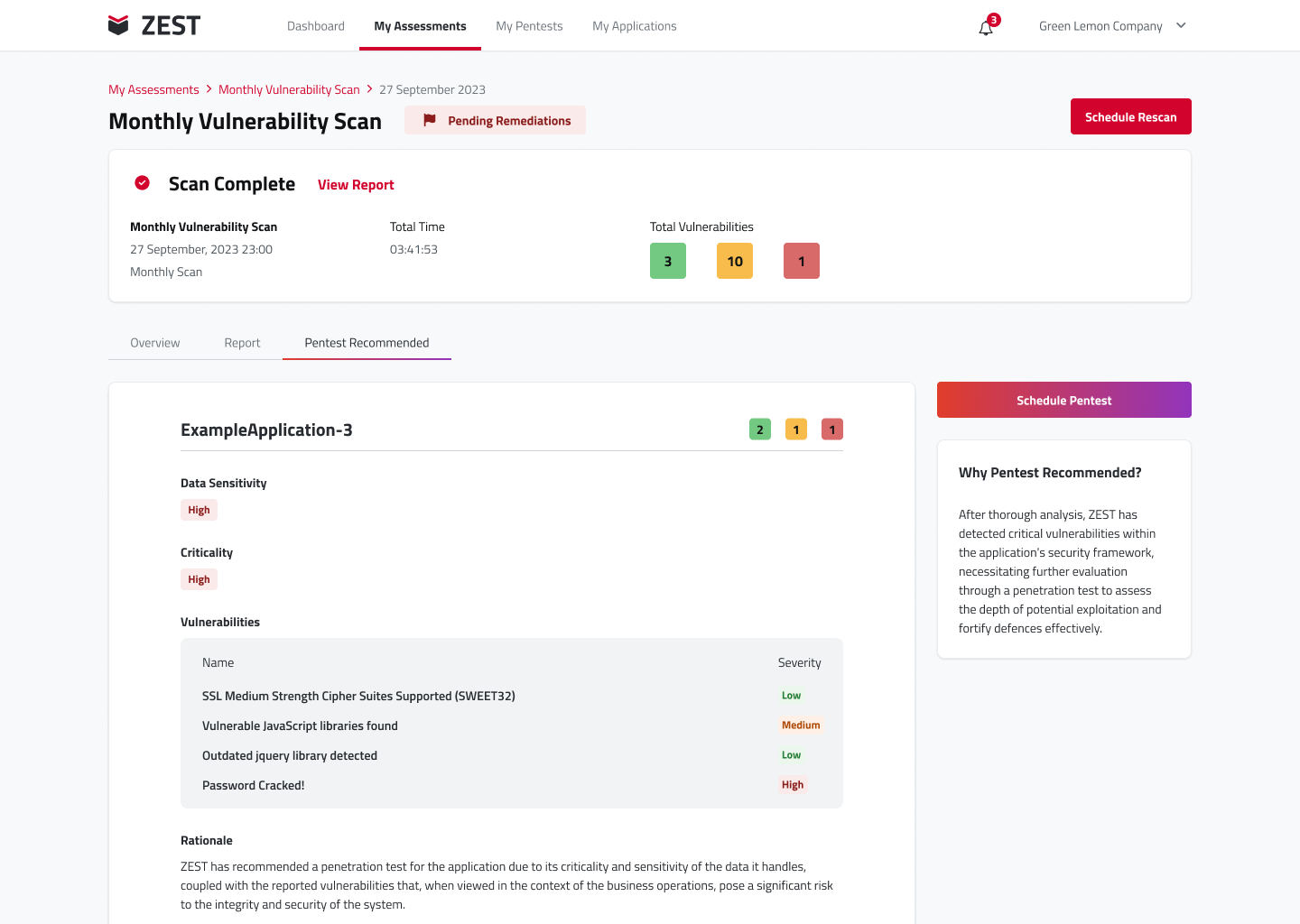
- Find and Fix: Built in remediation workflow to proactively address vulnerabilities and schedule rescanning to validate the patches.
- Schedule and relax: Schedule scans or conduct manual penetration testing with experts through a single interactive page allowing the evaluation of security measures through simulated cyber-attacks.
- Social Engineering: Create social engineering scenarios to train and educate human assets on simulated phishing exercises.
- Keep Informed: Live threat feeds to stay informed about the latest security threats and developments.
Key Benefits
- Benefit from a centralized platform that offers comprehensive security oversight, allowing you to monitor and enhance the security posture of all applications and assets from a unified interface.
- Achieve ISO 27001 compliant standards by easily configuring scans for groups of applications and assets, enabling instant, scheduled, or recurring assessments as needed, providing flexibility and convenience in managing security assessments.
- Comprehensive vulnerability coverage to ensure all aspects of digital assets are thoroughly assessed for vulnerabilities with: Web App, SAST, DAST, API and Infrastructure scanning.
- Leverage AI-driven reporting enhancements to streamline analysis, reduce false positives, and prioritize vulnerabilities. Proactively manage vulnerabilities with a remediation workflow that facilitates prompt mitigation and scheduled rescanning for remediation validation.
- Swiftly schedule manual penetration tests to evaluate security measures through real-world cyber-attacks, identifying and addressing vulnerabilities before they are exploited in the wild. Additionally, create social engineering scenarios to raise security awareness among employees and mitigate the risk of successful social engineering attacks.
- The solution offers flexibility in deployment options, allowing organizations to choose between on-premises, cloud-based, or hybrid solutions. This flexibility enables organizations to deploy the solution in a manner that best suits their infrastructure and security needs. - Customise assessments with the ability to pick and choose different tools and scan templates to align precisely with requirements and conduct different types of security evaluations, ensuring a tailored approach that addresses specific vulnerabilities and compliance standards. (edited)
Key Benefits
You can use ZEST for seamless integration into both the software development lifecycle (SDLC) and continuous integration/continuous deployment (CI/CD) pipelines, fostering a security-conscious development approach.
By incorporating security checks throughout the development process, ZEST ensures that security is prioritized at every stage, advocating a proactive security stance that emphasises preventative measures over reactive responses to potential breaches.
You can easily run instant, one-time or routine security assessments as ZEST has flexible scheduling capabilities for conducting vulnerability scanning. Driven by an advanced, yet simple to understand scoring system based on a nuanced evaluation of application risk profiles, ZEST optimizes resource allocation, focusing scanning efforts where they are most needed while minimizing unnecessary overhead.
Utilising AI, ZEST streamlines vulnerability management by normalising data, prioritising vulnerabilities, and identifying relationships between vulnerabilities. This AI-driven approach not only improves the efficiency of vulnerability identification but also reduces the likelihood of false positives, enabling security teams to focus on the vulnerabilities that matter.
In addition to systematic scanning, penetration tests can be scheduled, and social engineering exercises can be configured to assess human as well as technological assets to ensure your entire digital landscape is as robust as possible.
Other Solutions from Green Lemon Company Limited

Hyre