Best Practices to Reduce Attack Surface
There’s no doubt about it that 2020 was a decisive year for digital transition. But as organizations and businesses move their operations and services to the online world, they need to increase the focus on the attack surface to ensure their software is protected from malicious activities.
However, data seems to show the exact opposite is happening. According to a recent IDG survey commissioned by Insight Enterprises, although most of the companies inquired confirmed they increased their investment in IT security to support the remote workforce needs, 80% of senior IT and IT security leaders stated their organizations lack sufficient protection against cyberattacks.
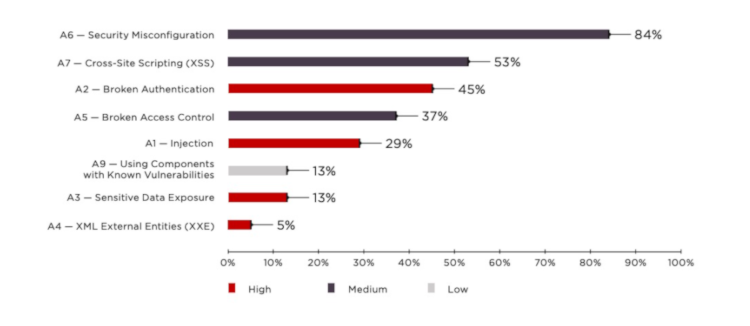
As for the most common vulnerabilities, a Positive Technologies report showed that one out of every five applications contain security misconfigurations, including sensitive cookies without the HttpOnly and Secure flags, that allow attackers to hack a user session. Cross-site scripting, broken authentication, and access control are also the topmost common vulnerabilities.
Most Common Types of Attack Vectors
Before we dive into the best practices to reduce the attack surface, we need to understand the most common types of attack vectors.
Quick note: Although attack surface and attack vector are related and often used interchangeably, they are not the same thing.
Attack surface is the sum of possible points that an attacker can use to enter your application or system.
Attack vector is the path an attack uses to access your application or system.
- DDoS (Denial of Service): A DDoS is an attack where a hacker makes your app stop responding usually, using one of four methods: TCP Sync, Teardrop, Ping of death, or Botnets.
- Password: The attacker compromises your password by unleashing a brute force or a dictionary attack against your application to guess the user password and log in as a legitimate user.
- Session Control: Session control typically happens while the user is logged in; the attacker launches an IP spoofing in the back-end of the app and, by doing so, can imitate the legitimate user’s IP address and disconnect the original user.
- SQL Injection: SQL injection is a high-impact vulnerability that happens by manipulating input data fields using SQL queries in apps that use dynamic SQL on their front-end.
- XSS: Also known as Cross-Site scripting, XSS is achieved by exploiting existing scripts within an application to gain confidential information from cookies.
Best Practices to Reduce Attack Surface
If the attack surface is the sum of gateways that an attacker can use to enter your application or system, you need to keep it as small as possible.
To reduce the exposure of your application right from the very beginning, there are a few security considerations you should keep in mind in two different application phases:
- Design.
- Runtime.
This blog post is based on a recent Tech Talk I presented, so for a more detailed version, take a look at How to Reduce Your Application Attack Surface.
Security Best Practices When Designing Your Application
When designing an application, here are a few things you should include to increase your app’s security and reduce the attack surface:
1. Authentication
- Always enforce complex passwords and do not allow a user to try a password more than three times.
- Integrate your app with an identity management solution for a robust authentication process.
- Always use SSL encryption.
- Enforce secure cookies.
2. Authorization
- Use a fine-grained authorization mechanism.
- Use module level-authorization and not just app-level authorization; you should clearly define and enforce who should have access to perform what in the app.
- Always treat your app access control as rules and attributes.
3. Encryption
- Encrypt data at all times: in transit, while storing it, and at rest.
4. Secure Application Assets
- Follow an enforcement methodology instead of an entitlement framework: in other words, always enforce security instead of giving leniency to the user in the form of entitlement.
- Perform regular audits and maintenance tasks of your security app assets.
- Regular monitoring these assets for vulnerabilities.
Security Best Practices at Runtime
At runtime, here’s what you need to consider:
1. Data security:
- Always apply industry-standard procedures to ensure there's no data leak and safeguard the confidentiality of the data stored by the application.
- Encrypt the storage and database.
- Do not expose insecure SQL operations within your apps.
2. Infrastructure security:
- Use intrusion detection devices to make sure that you’re alerted when there's untraced access.
- Use distributed Denial-of-Services mitigation services from cloud providers or individual providers.
- Perform regular risk assessments to ensure compliance with industry standards.
3. Vulnerability assessment:
- Run OWASP vulnerability checks regularly.
- Perform penetration testing regularly.
- Do code analysis and reviews for any major release.
4. Security monitoring:
- Constantly monitoring security for running applications.
- Adopt a Security Information and Event Management (SIEM) framework to ensure you detect and are alerted to any potential breach to mitigate the risk.
Meeting High-Security Standards
In today’s digital world, there’s no room for error. But with these best practices in place, you'll be able to minimize your applications' vulnerability to cyberthreats and vector attacks right from the very moment you start planning your application.
To take your app security to the next level, you can use a high-performance low-code platform like OutSystems, which has built-in features infused with AI to help you maintain high-security standards, all with zero development effort.
To learn more about OutSystems security offer and see it in action, take a look at How to Reduce Your Application Attack Surface webinar, where my colleague Krishnakumar G and I show you additional tips and tricks to avoid the most common security vulnerabilities. Take a look!