Enterprise-Grade Security & Compliance
Low-code security: What IT managers need to know

Anya Syulina June 28, 2024 • 7 min read

Subscribe to the blog
By providing my email address, I agree to receive alerts and news about the OutSystems blog and new blog posts. What does this mean to you?
Your information will not be shared with any third parties and will be used in accordance with OutSystems privacy policy. You may manage your subscriptions or opt out at any time.
Get the latest low-code content right in your inbox.
Subscription Sucessful
Security is on the mind of all IT professionals. Therefore, it’s no surprise that when evaluating low-code, they are sure to ask, “Is low-code secure?” In this blog, we’ll answer this question and others that IT managers like you have about low-code security and where it fits in the state of software development security today.
The state of software development security
Unless you’ve been living way off the grid, it’s not news to you that cybercrime is growing and getting more sophisticated as businesses enter into new stages of digital maturity. Unfortunately, a cybersecurity workforce talent gap is making it difficult to defend data, cloud environments, and more from attacks. DevSecOps offers some relief because it moves security closer to development, but it is only just maturing. Let’s look at these two challenges a little more closely.
1. It’s a great time to be a cybersecurity pro
According to an ISC2 report, there were 3.9 million unfilled cybersecurity jobs in 2023. An increase in cyber crime fueled by generative AI (GenAI) for sophisticated attacks is fueling demand for security experts much faster than industry and universities can deliver raw talent. It’s a great time to be a cybersecurity pro and a terrible time if you’re trying to hire one.
Gartner’s advice on how to plug this cybersecurity talent gap is to use GenAI “to help solve a number of perennial issues plaguing cyber security, particularly the skills shortage and unsecure human behavior.“ And Coursera recommends the use of intelligence to reduce the number of false positive alerts and to automate manual log reviews and other repetitive tasks.
2. DevSecOps is maturing, but it has a long way to go
Between an uptick in ransomware attacks, lack of clear boundaries for organizational data, and increased risk with collaborative citizen development, DevSecOps is more important than ever. In this approach, instead of security testing being a heroic effort late in the software delivery lifecycle, it’s baked in from the get-go.
More development teams have adopted a “shift-left” mentality, taking responsibility for security from requirements gathering and analysis all the way to testing. However, embedding security in several stages of the app lifecycle is not easy for those who are not trained in DevSecOps.
The fact of the matter is that IT leaders have an uphill struggle. On one hand, recruiting developers with the necessary DevSecOps skills is hard. On the other, training existing staff to infuse security practices into the entire lifecycle takes time and perseverance. Because of the need for faster releases and performance speeds, slowing either down to meet security priorities could even be career limiting.
Fortunately, there is a third option.
Fear not: Low-code is here
In a recent article based on original research, KPMG named security as one of the top obstacles to adopting low-code.
Why is security seen as an obstacle?
The reason for this “fear” has to do with the fact that low-code platforms abstract code, which is perceived as sacrificing security posture, such as vulnerability, threat, and error prevention, for speed. This is especially true when we’re talking about development platforms that cater to business users (the so-called citizen developers). Also, most low-code and no-code platforms interpret models, so there is no underlying code to review for vulnerabilities or issues.
Another reason that security is an obstacle is because many in IT have the idea that low-code development requires even more specialized cybersecurity practitioners than DevSecOps. There is also a fear of time lost if entire development teams need to be trained on low-code security while IT backlogs continue piling up.
How low-code can help
The truth is, however, that low-code has a place in today’s software development security landscape. In fact, contrary to popular opinion, traditional application development doesn't always take security into account either. Or, someone puts it in place later.
By contrast, even the most basic low-code platforms today offer security protections. Controlled development environments, pre-vetted components and integrations, automated security checks, and a reduced attack surface help protect against malware and ransomware. Low-code platforms can also automatically test for vulnerabilities and performance. This automation reduces manual security steps and significantly increases developer productivity.
Also, in some low-code platforms, basic governance and controls are in place out of the box, before anyone starts tinkering with application development. Many have built-in authentication methods, standardized encryption implementation, automated session management to prevent unauthorized access, hijacking, and data privacy issues. They can also lower the number of security incidents caused by misconfigurations because they provide pre-configured templates and standardized configurations, and they reduce manual intervention. In addition, built-in compliance features, standardized processes and documentation, and easier implementation of security controls can prevent failed audits.
But how secure is low-code for the enterprise?
Now, for enterprise security use cases, the most basic low-code platforms might not be enough. If you’re dealing with highly regulated industries, like finance and healthcare, you need to ensure the development platform is compliant with certain regulations.
Many low-code platforms aren’t. For example, with a regular low-code platform-as-a-service, updates that the vendor implements might not be consistent with your security policy. Even big names like Microsoft have had their challenges.
Also, an enterprise full of citizen developers needs special security care and feeding. These citizen developers may be highly technical people, but they don’t have the experience or expertise of professional developers to be sensitive to the security liabilities and interdependencies between applications.
Also, security needs to be managed apart from typical development. When developers are tasked with innovation at a high speed, they are often not incentivized to prioritize security. Having someone, or a platform, manage security is a notable asset.
It also doesn’t help that not all low-code platforms provide the same features or cover the same use cases. I discussed that in my previous blog post about the low-code market, where I explained the difference between regular low-code and enterprise-grade low-code like OutSystems. And security is one of the main differentiators between these two groups of low-code platforms.
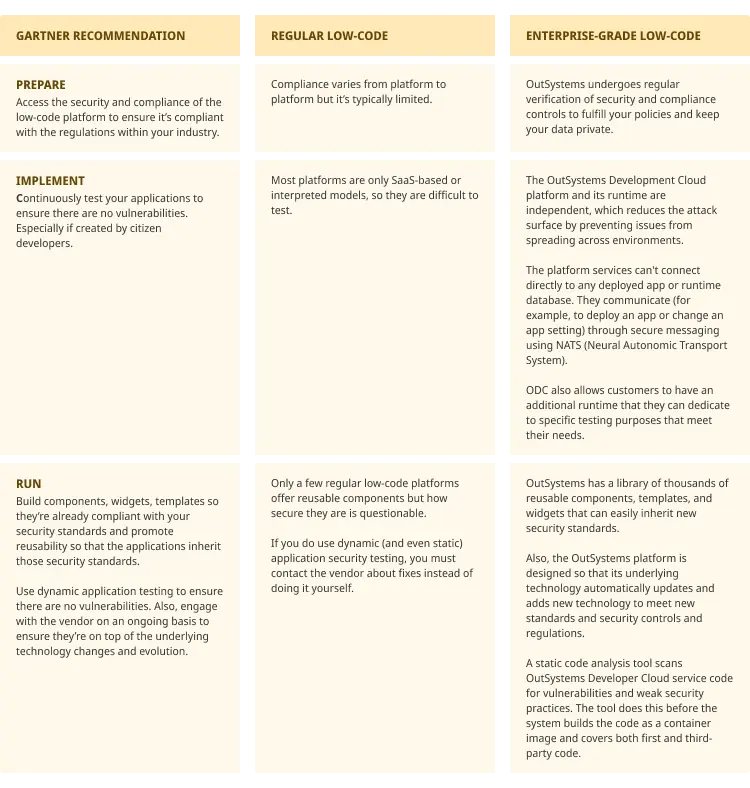
To give organizations some peace of mind, Gartner has a list of recommendations you can follow from the moment you start evaluating the right low-code platform to the development process1. In this table, I compare regular low-code to the OutSystems Developer Cloud platform based on Gartner's recommendations for secure low-code.
Learn more about low-code
This is just a sneak peek of how OutSystems high-performance low-code protects your applications and users. To read about all of our security features take a look at these additional resources:
And to learn more about our platform, take a look at our platform page and feel free to schedule a demo. Our experts are here to clarify any questions you may have.
1How to Mitigate Vendor Lock-In, Technical Debt and Security Risks of Low-Code Development, by Jason Wong, Gartner 2022.
Anya Syulina
Anya Syulina has over 18 years of experience applying a customer-first focus across a diverse range of industries — from consumer goods to mobile games and enterprise SaaS. Now she is putting her knowledge and customer-centric expertise to work as a Product Marketing Manager at OutSystems. She says she accidentally moved to Portugal following a dream and she's passionate about knitting.
See All Posts From this authorRelated posts
Anya Syulina
June 27, 2024 7 min read
Pauline Harlinghausen
September 21, 2023 4 min read
Forsyth Alexander
July 19, 2024 7 min read



